C++ inscription in abstract digital background. Programming language, computer courses, training. Stock Illustration | Adobe Stock
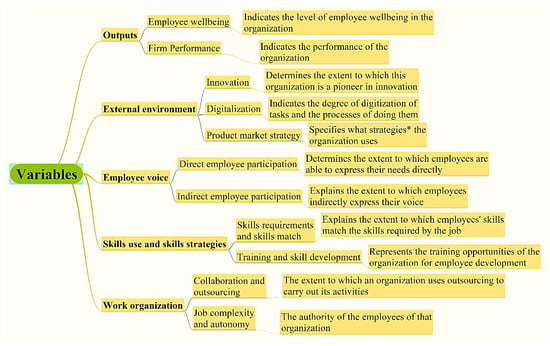
Algorithms | Free Full-Text | Correlation Analysis of Factors Affecting Firm Performance and Employees Wellbeing: Application of Advanced Machine Learning Analysis

Training for new generation of facilitators from Europe and North America - intangible heritage - Culture Sector - UNESCO

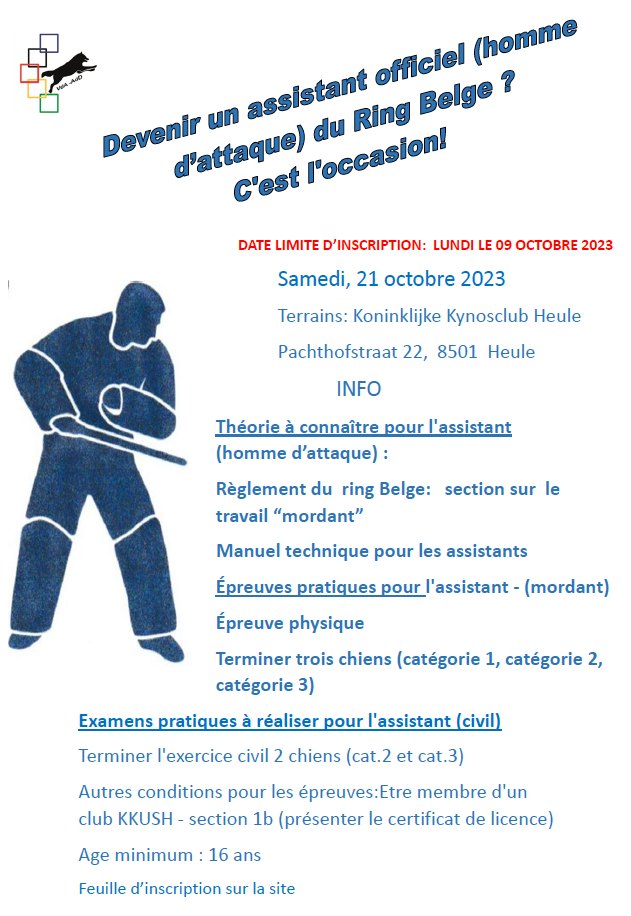
SET Online Karate Canada: 2023 Canada Open Karate Championships - Coach Registration | Championnats ouverts de karaté du Canada 2023 - Inscription des entraîneurs·es

BIG BORED BELGIAN BRASS BARRELED BLUNDERBUSS Coach Gun 19th Century Antique With MM Company Inscription on the Barrel! for sale
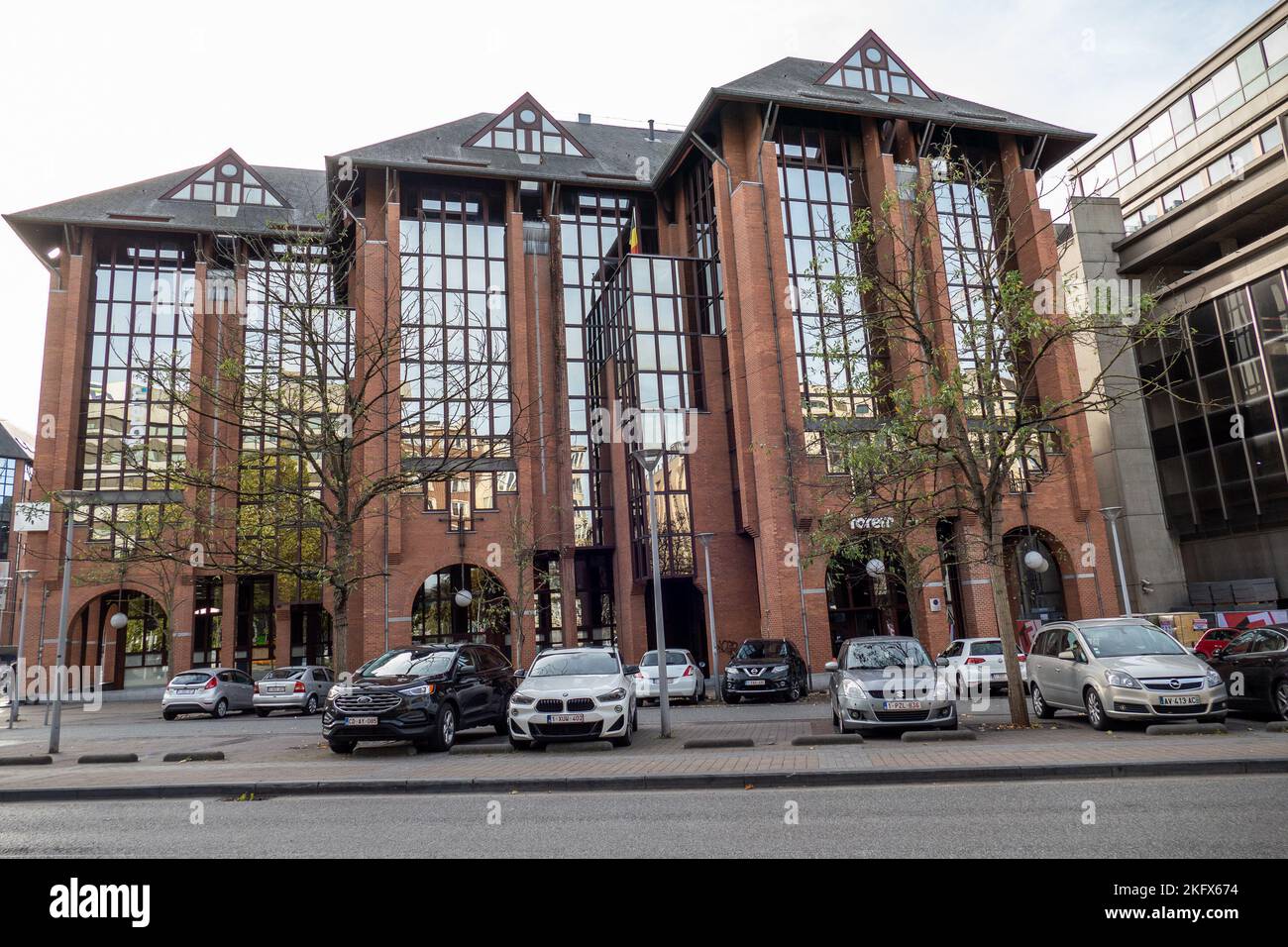
Charleroi, Belgium, November 11, 2022. Forem is the Walloon office for vocational training and employment Stock Photo - Alamy

BIG BORED BELGIAN BRASS BARRELED BLUNDERBUSS Coach Gun 19th Century Antique With MM Company Inscription on the Barrel! for sale
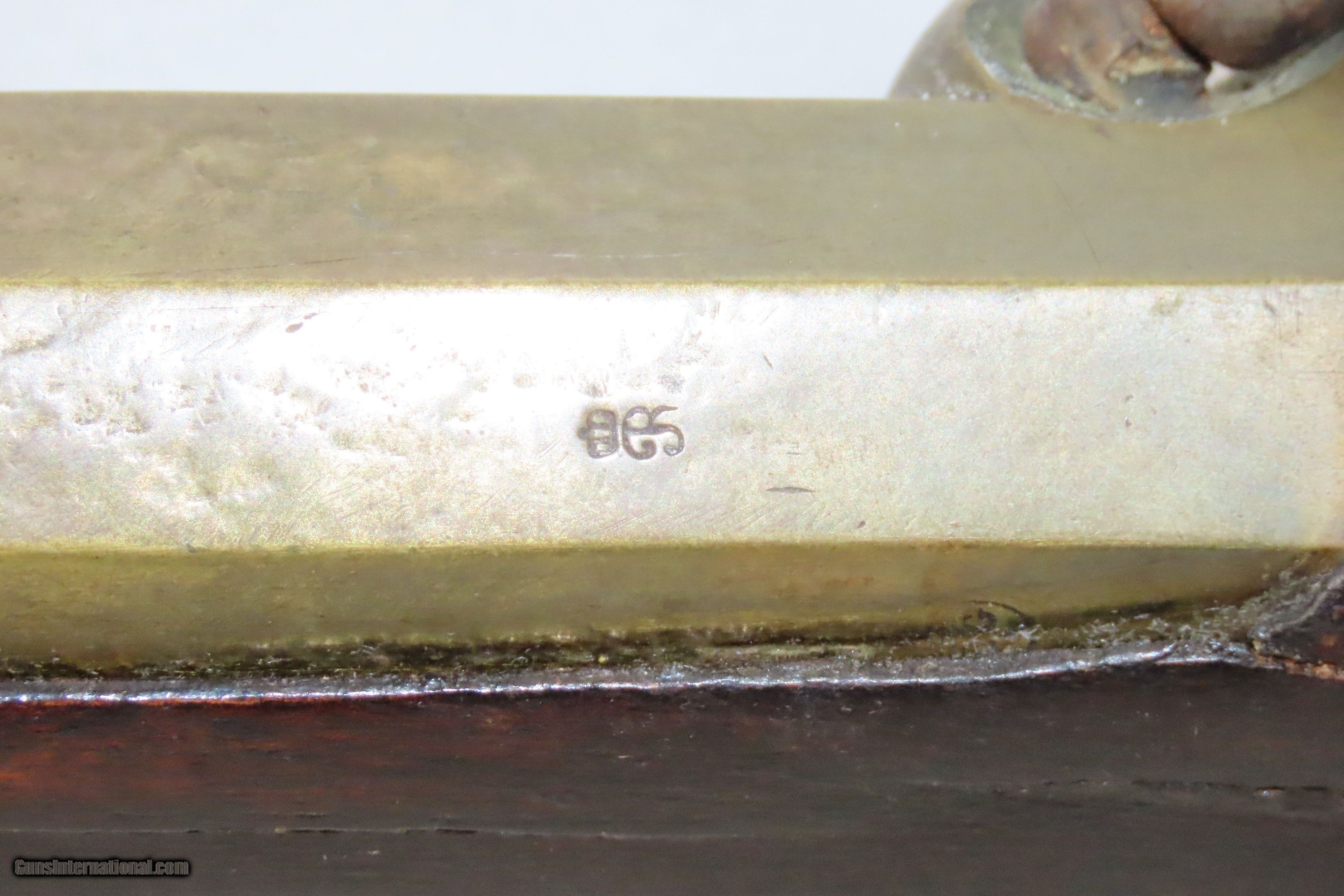
BIG BORED BELGIAN BRASS BARRELED BLUNDERBUSS Coach Gun 19th Century Antique With MM Company Inscription on the Barrel! for sale